Eighty-five years ago, Secretary of State Henry L. Stimson was presented with a Japanese telegram that had been decoded by a group of skilled cryptologists. Stimson was horrified at the moral invasion represented by the deciphering of another nation’s private communication, and he cut off funding to the Cipher Bureau. According to the National Security Association (NSA), Stimson famously admonished cryptologists, “Gentlemen do not read each other’s mail.”1
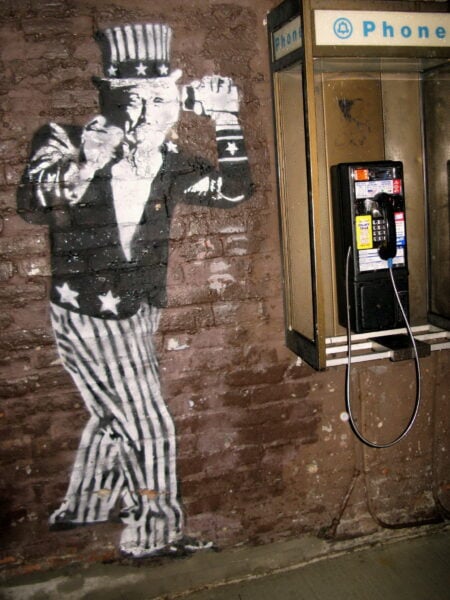
Photo by Jeff Schuler (www.flickr.com/photos/jeffschuler), CC-BY 2.0.
Of course, the United States eventually regrouped, and in 1952, drawing on the technological advances of computers and electronics, it reformed the Cipher Bureau under the auspices of the once unacknowledged, but now altogether familiar National Security Agency (NSA). Sixty years later, Edward Snowden revealed exactly how far the American government has ventured past Stimson’s original Maginot Line, going far beyond diplomatic cables and exploiting huge collections of data from social media, e-mail, video, file transfers, and video and voice chats of average Americans. The fallout has been unending, and many Americans have reacted with a deep sense of distrust of Silicon Valley tech firms. In the words of Facebook CEO Mark Zuckerberg, “The NSA made people distrust us.”
Enter Snapchat, a mobile app that lets users take photos or short videos and then decide how long those messages will be visible once they are opened. Snapchat messages can have a life span of up to 10 seconds, and after the message expires, it supposedly disappears forever (more on this later).
In the beginning, the service appealed mostly to teenagers looking for more private ways to send and receive rather questionable pictures and messages, but it has evolved into a significant touchstone in 21st-century public culture, where we see adults actively seeking new apps to privately screen their communications. Indeed, Snapchat has spurred a whole new genre of self-destructing communication apps, including Poke (created by Facebook), Wickr, Confide, and Hash, to name only a few. These apps market themselves as solutions to the potential pitfalls of having a digital footprint—promising to allow users to communicate with loved ones and friends without fear that every communication will be archived and available in a Google search or, worse, the government’s prying eyes. According to Nico Sell, cofounder of Wickr, “It’s natural for us to go back to it [unarchived communication] for things like communicating with our friends and family, and not having to think about the fact that the Internet is forever. Ephemeral data is the future.” According to preliminary (anecdotal) data, Wickr boasts more than one million downloads, and is used primarily by human rights activists, lawyers, journalists, and (because Wickr is HIPAA compliant) some hospital and medical staff.
What does all of this mean for historians? The move toward ephemeral messaging services puts historians in an all too familiar place. Just a few years ago, the rise of social media also brought new questions regarding how archivists would preserve social media content, and led government institutions like the National Archives and Records Administration to establish best standards for federal social media record keeping. But now we must contend with a growing population of adults who are averse to both print and permanent records. No one knows for certain whether this trend will last, but as of now, the ephemeral social media trend is a multibillion-dollar industry that continues to gain steam.
So the first question we must ask is: do these bits of data actually disappear as programmers promise? Not really. In the case of Snapchat, photos and video are not deleted, and even remain on the individual’s device. Instead, Snapchat applies an encryption (reminiscent of a cipher or code, ironically) that tells an operating system to ignore the data—a Silicon Valley smoke-and-mirrors ploy. Wickr touts its “military-grade encryption” software that acts as a virtual “secure shredder” and claims the software makes it impossible for data to be recovered. Thus, depending on the app, the plausibility that data is truly deleted is a matter still up for debate.
Aside from the question of whether these messages are really ever deleted, the ephemeral social media trend should provoke wider discussions. Should individual privacy always supersede the future needs of historians? Is ephemeral social media the type of source material archivists should consider preserving? Or perhaps this trend is merely a reminder of what historians already know: that many historical records are carefully crafted and curated by their creators as they edit out all the embarrassing bits. In the rush to cover their tracks, social media users aren’t asking the sorts of questions that come naturally to historians and archivists, so the phenomenon of self-destructing social media offers an opportunity for both professions to make the case for the importance of preserving something for future generations.
Note
- The quote is from Henry L. Stimson’s and McGeorge Bundy’s On Active Service in Peace and War, in which Stimson justified his action. See also David Kahn’s The Codebreakers: The History of Secret Writing. [↩]
This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License. Attribution must provide author name, article title, Perspectives on History, date of publication, and a link to this page. This license applies only to the article, not to text or images used here by permission.