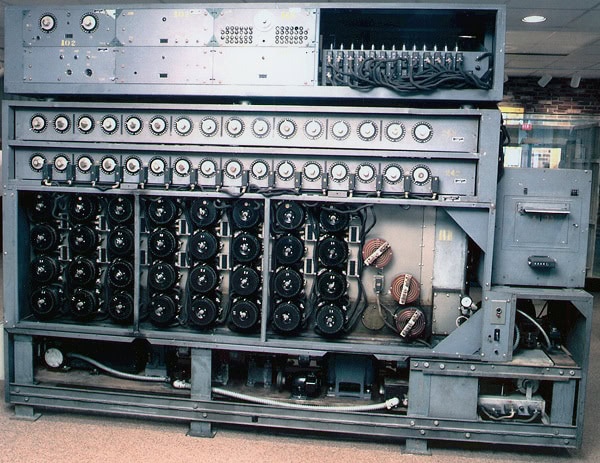
US Navy Bombe used to decrypt messages from the German Enigma machine during World War II. National Security Agency/Wikimedia Commons
At the 16th biennial Symposium on Cryptologic History, held this past October, William F. Friedman was a celebrity of sorts. The famous US Army cryptographer’s name was on everyone’s lips—at plenaries, breakout sessions, and in side conversations around the lunch table.
This is to be expected at a meeting on the history of cryptology—the National Security Agency (NSA) credits Friedman, who passed away in 1969, with pioneering the use of scientific principles to make and break codes and for shaping much of the work being done in signals intelligence and information systems security today. (His wife, Elizebeth Smith, was an important cryptographer in her own right.) Adding to his fame, two years ago, the NSA declassified a huge batch of documents from the William F. Friedman Collection of Official Papers. The release of over 52,000 pages included materials spanning almost 60 years that, according to the NSA, shed light on “both the career of this legendary cryptologist and the history of American signals intelligence.”
But Friedman’s ubiquity at the two-day symposium reflects a greater truth about intelligence work: it is deeply indebted to the work of the code breakers who came before, and that cryptologic history should inform intelligence work being done today.
The Symposium on Cryptologic History is organized by the NSA’s Center for Cryptologic History (CCH) and the National Cryptologic Museum Foundation. The CCH provides historical support to the NSA to improve decision making and presents historical accounts of cryptology to the intelligence community, government agencies, academia, and the general public. The National Cryptologic Museum Foundation supports the National Cryptologic Museum, which it describes as the “first public museum in the US Intelligence Community.”
According to John A. Tokar, chief of the CCH, cryptology consists of both creating codes or ciphers to protect one’s own communications” (cryptography) and “solving another entity’s codes or ciphers without prior knowledge of the system key” (cryptanalysis). The theme of this year’s symposium—“Milestones, Memories, Momentum”—referred to the events of the 20th century that were important to the history of cryptology. In 2017, for example, cryptologists marked the 75th anniversary of the Battle of Stalingrad, the 75th anniversary of the Germans introducing the most advanced Enigma machine, and the 100th anniversary of the Zimmermann telegram, an important piece of signals intelligence during World War I. These “milestone events and advances in cryptology, as well as how we remember their significance,” the CCH’s symposium webpage noted, “provide momentum to create the systems of today and the future.”
In addition to historians, who attended as speakers and participants, the conference also drew intelligence and military officers, directors of national security agencies, computer scientists, mathematicians, journalists, communications and English professors, and curators. The federal agencies represented at the symposium included the Central Intelligence Agency, the National Archives and Records Administration, the Department of Defense, the Federal Bureau of Investigation, US Cyber Command, and, of course, the NSA.
Attendees were drawn to the symposium for a variety of reasons. Some retired NSA officers were there to continue a long tradition of attendance; others hoped to use the gathering to request support or leads for their research. Almost everyone, however, was driven by the belief that researching and writing about cryptologic and intelligence history is important because of the potential to make new discoveries and to shape what we remember about the past.
General Michael V. Hayden, former director of the CIA and the NSA, for example, stated during the first day’s plenary—titled “Writing about Cryptology and Intelligence: Challenges and Opportunities”—that it’s crucial for individuals like him, with insider knowledge of how national security agencies function, to write the histories of these institutions. Otherwise, he suggested, they risk ceding them to less discerning authors. The plenary also highlighted other challenges facing those writing about intelligence: difficulty accessing sources, a lack of faith in the declassification process, and agency requirements to review and, in some cases, omit sensitive information from final manuscripts. Panelists also discussed how to market books on intelligence history to diverse audiences and specialists in other fields.
Several panels and presentations at the symposium focused on World War I, World War II, and the Cold War. In the panel “Breaking Enigma,” scholars discussed the intelligence contributions of the Polish people before and during World War II. They particularly focused on Polish success in breaking German cipher machines before the war, and how cooperation among British, French, and Polish agents led to British code breakers cracking Enigma during the war.
“The study of history is in many ways the same as the production of intelligence.”
A panel on women in cryptology affirmed the contributions of women code breakers. Two speakers discussed Elizebeth Friedman’s contributions to US war efforts, and Jackie Uí Chionna, a historian at the National University of Ireland, Galway, presented new research on Emily Anderson, a 20th-century Irish code breaker and music historian about whom little writing has been done. Liza Mundy, a senior fellow at New America and author of Code Girls: The Untold Story of the American Women Code Breakers of World War II (2017),emphasized the larger significance of recovering the story of the army “code girls” working in the Washington, DC, area during World War II. Losing their work in code breaking, said Mundy, would also mean losing their contributions to technology—women were crucial pioneers in the fields of cybersecurity and computing, and discussions about women’s place in tech should be informed by this history.
Panels also highlighted global cryptologic history. Gregory J. Nedved, a historian at the CCH, discussed his ongoing research on the role of cryptology in the Sino-Japanese War of 1894–95. Contrary to accepted wisdom that code breaking by Japan had been crucial to its success over China, Nedved argued that it was not as helpful on the battlefield as other forms of intelligence or as useful in treaty negotiations to end the war as has been previously argued. Other presentations focused on China’s use of tactical deception in warfare historically, and the Austrian Black Chamber, an office tasked with intercepting mail and translating or deciphering incoming messages during the 18th and 19th centuries.
Cryptologic history, however, is about more than war. Katherine Ellison, professor of English at Illinois State University, presented her research on how pedagogical manuals on ciphering revolutionized literacy in the 17th century. In her book A Cultural History of Early Modern English Cryptography Manuals (2017), Ellison quotes a 17th-century Englishman on the popularity of ciphering and deciphering among the public. In her presentation, she highlighted how these manuals taught people a different way of reading, reminding them to look beyond the content of a text to its visual appearance, size, and graphics. Ciphering manuals, Ellison argued, taught a generation that was “reading more than ever before how to read.”
Work presented at the symposium also addressed questions about the value of history, particularly the importance of history to intelligence. At a lunch presentation aptly titled “The Essential Role of History in Intelligence,” Richard W. Stewart, acting director and chief historian at the US Army Center of Military History, outlined the connections between history and intelligence. “The study of history is in many ways the same as the production of intelligence,” he said. For one, both require going back to the primary sources. And when combined with new information, archival records can provide refreshing insights into intelligence. Stewart called on both historians and intelligence officers to help senior government officials and the public understand the value of their work.
Stewart’s presentation also touched on another reason history is so important to intelligence work—a reason reflected in the continued conjuring of William Friedman’s name during the symposium and the continued fascination with the achievements of cryptanalysts during World War II. History inspires intelligence production, Stewart reflected, and “intelligence analysts and agents are, quite rightly, inspired by the stories of those who have gone before.”
This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License. Attribution must provide author name, article title, Perspectives on History, date of publication, and a link to this page. This license applies only to the article, not to text or images used here by permission.